WHY CRYPTO IS IMPORTANT FOR MODERN SOCIETY
Cryptography is the science of protecting communication, information and data from unauthorized access. Wherever telecommunication happens, cryptography is usually applied. It plays the crucial role of protecting privacy, and critical or even classified information. For example, it provides digital signatures to financial transactions, and prevents both eavesdropping and tampering.
Cryptography is truly a pillar of our increasingly digital reality.
QUANTUM THREAT
The race against quantum computers is on. The revolutionary quantum computing paradigm poses an immediate threat to most of the deployed asymmetric encryption technology. The store-now-decrypt-later attack, which is already happening across the globe, jeopardizes the confidentiality of sensitive communication today: If the secure shelf-life of the data exceeds the arrival of sufficiently powerful quantum computers, data will be exposed and the time to act is now.
MATHEMATICAL THREAT
Encryption has historically been a back-and-forth between new encryption methods and the challenge of cracking them. If an attacker is careful enough, they can hide for a long time while accessing the compromised data. Today’s encryption algorithms – including post-quantum cryptography – are based on assumptions rather than proofs and could be broken at any time by new mathematical developments.
COMPUTATIONAL THREAT
Supercomputers and data centers exist around the globe for decrypting and storing data. As of today, the growth of computational power according to Moore‘s law and the increasing density of data storage seems unbroken. Both pose yet another threat to deployed cryptography, forcing re-deployment of existing infrastructure. In conjunction with the quantum and mathematical threats, the computational threat shapes the ever-growing options of your adversary.
GOVERNMENT
Handling classified digital information is indispensable for every modern government. At the same time, long-term communication secrecy has never been more challenging on the national and pan-European scope.
TELECOM
Telecommunication touches the core of all of our private lives. Protecting the right of privacy is an European ideal that requires more dedication than ever, as states and companies become more hungry for data.
INFRASTRUCTURE
Our society and culture is critically dependent on infrastructure such as the energy grid, banks, healthcare, navigation, and the telecom backbone. Protecting the control layer is a growing challenge as the critical infrastructure is targeted by adversaries.
INDUSTRY
Corporate confidential data exchange is essential in a highly competitive international playing field where the gloves are off. Trade secrets keep the competition in check, and keeping the secret requires high confidence in communication channels.
Our SolutioN – Integrated QKD
QKD is a paradigm shifting cryptographic key exchange method since it provides long-term security.
CV-QKD is a paradigm shifting implementation since it can be realized using components and processes that are widely adopted across the telecom industry. No exotic components like single photon detectors are necessary.
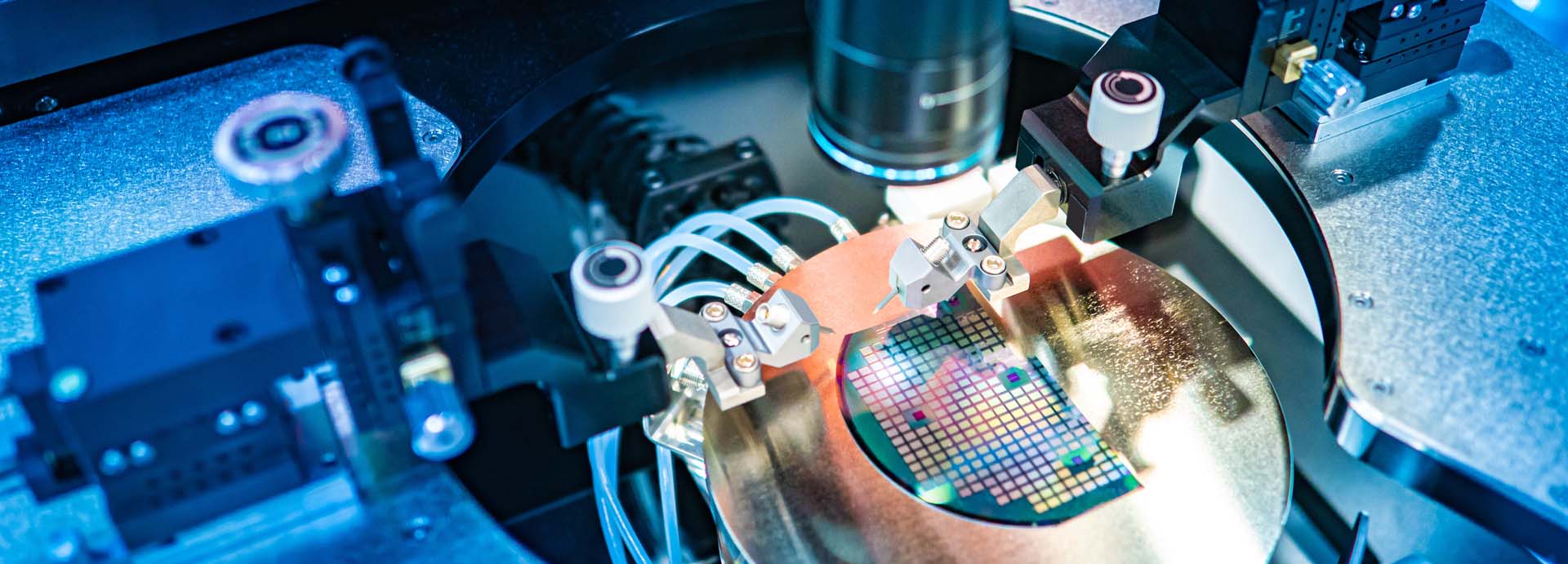
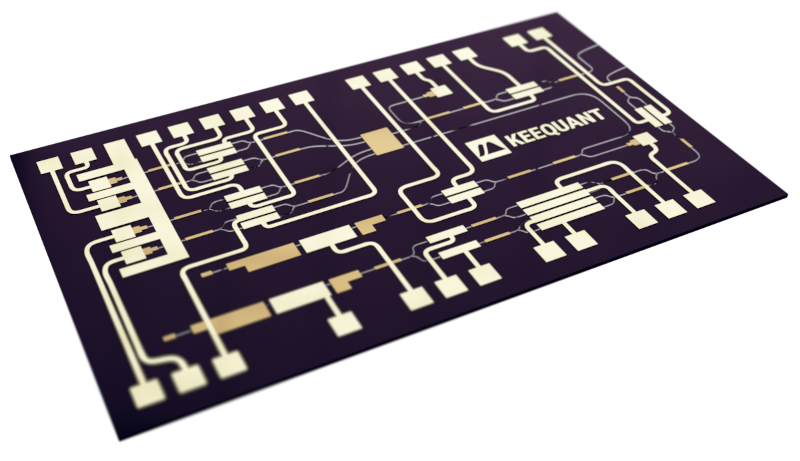
KEEQuant leverages the huge potential of Photonic Integrated Circuits (PICs). 100% of the CV-QKD functionality will be hosted on a single PIC. The relevant technical properties such as size, weight, power consumption, environmental requirements, but especially producibility and cost of QKD systems will become similar to today‘s telecom devices.
Our long-term vision is to make CV-QKD an integral part of tomorrow‘s standard telecom transceivers – a true commodity with no extra hardware cost.